20 Top Pieces Of Advice For Selecting Windows 11 Kaufen Shops20 Top Pieces Of Advice For Selecting Windows 11 Kaufen Shops
Microsoft Office And Windows Licensing For Small Businesses: Affordable Alternatives. It's about strategic investments that minimizes long-term risk as well as ensures compliance and grows with the business. The combination of grey-market Windows 11 OEM keys as well as separate Office lizenz purchases leads to a shaky and unsecure IT infrastructure. True cost-effectiveness comes from understanding the ways in which Windows licensing, Office subscriptions, and even security tools interact to form a coherent system. This guide moves beyond simple price tags to explore the ten most important aspects to consider when building a professional, sustainable and ultimately cost-effective software system for a growing company, connecting choices that are made from desktop OS, server access, and security.
1. Windows 11 Home has no place in a company.
The most frequent and costly mistake is buying a cheap Windows 11 Home key for a business workstation. Windows 11 Home lacks BitLocker security for sensitive data, cannot join Active Directory or Azure Active Directory and doesn't offer Local Group Policy to control IT. Also, it forces users to install disruptive updates. For any machine handling information for business, windows11 lizenz` must mean Windows 11 Pro. Security, management and professionalism aren't an option despite the relatively low price of Windows 11 Pro. Businesses operating under Home licenses is using a consumer grade infrastructure, which poses an essential risk.
2. Calculator to calculate "Hardware Refresh".
When you `windows 11 kaufen for business and business, the OEM vs. Retail decision has long-term financial consequences. The OEM license might be less expensive initially, but will end on the first computer the license is installed on. Retail licenses can be transferred. OEM can make more sense for disposable budget PCs. For higher-end workstations or if you upgrade components individually, Retail licenses save money over time. Calculate the Total cost of Ownership (TCO). Retail licenses are $200, with OEM Pro at $140. If the lifetime cost of your PC is $800, then the retail premium is a bargain to ensure future flexibility.
3. The Microsoft 365 Ecosystem: Where Real Cost-Effectiveness is Real.
The era of a one-time office lizenz purchase (like Office 2021) is ending for dynamic businesses. Microsoft 365 Business Premium is about $22. This bundle is often the best value. It includes: Windows 11 Pro upgrade rights (solving your `windows 11 lizenz kaufen` need), the full Office suite, 1TB OneDrive cloud storage, business-class email, and–crucially–Intune for device management and Azure AD for identity. The single subscription will allow you to upgrade and legalize your entire desktop stack. It also includes management tools that are not offered by standalone products. It transforms capital costs into a predictable cost for operating.
4. Windows 7 Upgrade Path – A compliance and security mandate
Businesses who cling on the old version of "Windows 7" are atop a time bomb of unsupported applications. Upgrading doesn't just mean the addition of new features. It also means security and compliance. It's not about purchasing an entirely new "Windows 11 license". It's a chance to reconsider the whole software strategy. The transition from Windows 7+ perpetual Office to a Microsoft 365 Business subscription-powered device modernizes security and enables cloud backup. It also enables remote working. Not just the new OS key as well as the subscription fees are included.
5. Knowing "CAL" Shadow cost to future growth.
If you plan to require an on-premise server like `windows server 2025` for file sharing, databases, or line-of-business apps You must plan for Client Access Licenses (CALs). A CAL is required for each user or device accessing the server. It is an additional cost that is not included in your windows 11 professional desktop license. Small-scale businesses looking to grow should consider CALs as part of their budget for the long term. Windows 11 Home (which is not legally able to access the Windows Server when used in commercial situations) and use without a license creates an extremely high risk of not being in conformity during a Software Audit.
6. Bundling and Best-of Breed Security Integration
License complexity depends on the choice you make, Windows Defender (included), or a third-party software such as Kaspersky Premium or Norton360. Microsoft 365 Premium includes enhanced Defender Security as well as centralized Threat Management. A separate third-party software suite could be unnecessary, adding costs and administration overhead. Consistency is, however, is crucial when, for instance, you need to meet certain regulatory requirements or if a specific console from a third-party is the preferred choice. A solution that is less expensive and simpler to manage than a patchwork. The "cost" in security is usually the time to manage multiple systems rather than the subscription fee.
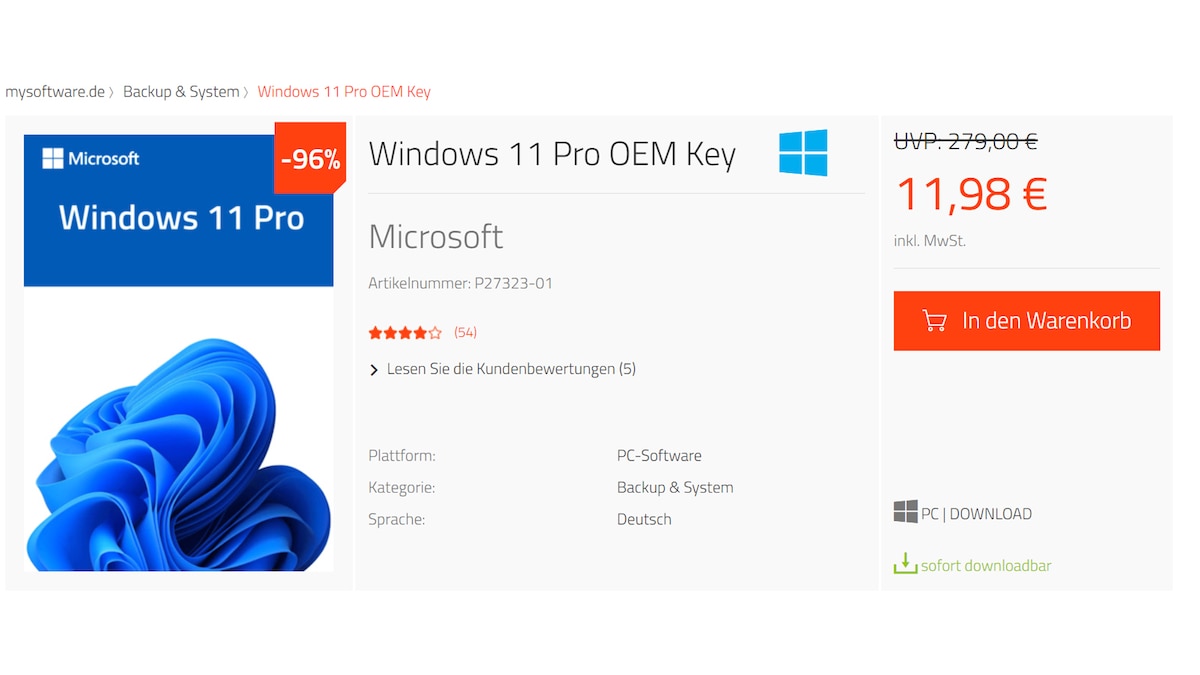
7. The Grey Market Trap: False Economicity in Licensing.
You will find prices that are too good to be true if you look on non-official marketplaces such as "office Lizenz" and "windows 11. These are usually volume licenses, OEM keys that violate the terms of another region. Microsoft may deactivate them leaving you unlicensed and insecure software, and the risk of being fined in the event of an audit. If you are a business, this represents an extreme risk, not funded. To ensure cost efficiency, it is best to buy from authorized distributors or Microsoft Cloud Solution Providers program (CSP) that guarantees complete support, upgrades rights, and the legitimacy.
8. Perpetual Office The Niche for Static and Air-Gapped Scenarios.
The standalone perpetual `office lizenzThe standalone perpetual office lizenz' (e.g., Office Professional 2021) remains a narrow business scenario. It is designed for a machine that doesn't require cloud services or an administration system. It will also run the identical features for at least 5 years (until it ceases support). This is a rare thing. Small businesses can benefit from subscription models provide more features particularly when it comes to tools for collaboration (Teams/SharePoint), cloud storage for files and mobile access. A perpetual license means locked-in software, stagnant services and reduced productivity.
9. Modeling Mobility The Device Based Model vs. User-Based Licensing.
The old licensing model was bound to a device. (One OEM Windows 11 license per computer). Modern licensing, as offered by Microsoft 365, is user-based. One user license is able to use up to five devices per user (PC, Tablet, Macbook or phone). It is very cost-effective for businesses who have mobile workers, hybrid workers, as well as those who offer a computer with a keyboard. You are able to license the user and not the computer. Be aware of the mobility of your employees when you design your licensing strategy. The use of a user-based subscription typically reduces the total number of licenses needed as compared to a rigid device-bound approach.
10. Making an Coherent stack for Audit-Ready.
The aim should be to create a legal, simple and documented software stack. Microsoft 365 Premium for Windows 11 Pro (per user), Office, Management Security + Retail, or OEM Windows 11 Pro Licenses for any device (e.g. kiosks) that are not covered by the subscription + Security postures that are consistent, controlled and managed (either via Defender in M365, or through a central, third-party application). This platform provides audit-ready capabilities that is flexible and reliable. The "cost" is the cost of chaos, incompatibility, data loss, inadequate security, and non-compliance. Follow the top rated windows 11 oem for site examples including microsoft office software key, ms visio software, microsoft office 2016, windows office software, outlook software download, ms office 2016, office 2019 professional plus, windows and office, microsoft visio, office 2016 software and more.
Understanding Windows Server 2025 And Client Access Licenses (Cals) For Business.
The transition from a peer-2-peer network into a centralized and managed IT infrastructure is an essential decision for any company that is growing. This transition can be costly, and the most common error is not paying attention to the Client Access Licenses. It's not an option, it's a cornerstone in the Microsoft ecosystem. Inability to properly license access to clients could cause a project to fail or even result in serious penalties during an audit. It also can create a complicated web of dependencies, which affects everything from the operating system for your desktop you select to your security and productivity tools. This guide explains the 10 interrelated concepts essential for any business to be aware of when planning Windows Server 2020. It illustrates how server licensing affects your entire desktop experience and the legality of it.
1. The Foundational Principle is: The Server License is Just the Entry Fee.
If you purchase a "Windows Server 2025" license, it gives you the ability to install and operation on a live or virtual machine. It is crucial to remember that this license doesn't give the device or user access to. The CALs are used to purchase this right in a separate transaction. Imagine buying a server licence to rent a venue or stage. In addition, you'll require a ticket (a User Cal) for everyone who enters to see the spectacle.
2. CALs & Desktop OS Legitimacy – An Inseparable pair
It is not legal to make use of a CAL on clients that run an unlicensed OS. If your workstations for business are activated with grey-market `windows 11 oem` keys on a windows 11 lizenz buy discount website buying legitimate CALs for the same is a contradictory, ineffective practice. Microsoft's licensing rules requires that the operating system which your client runs be properly licensed. An audit will first invalidate the desktop licenses, making the CALs–and potentially the server access itself–non-compliant. The entire stack from the desktop to the server, should be clean.
3. The User CAL The User CAL vs. Device CAL Choice: Modeling Your Workforce.
This is also a choice that will have financial consequences. A User CAL permits the user named in the CAL to connect to multiple devices (e.g. their laptop, desktop and tablet). A Device CAL is a license for devices that can be used by multiple users (e.g. shared workstations in factories). The most cost effective choice will depend on your usage patterns. The effectiveness of user CALs increases when a mobile workforce uses several devices. Device CALs are cheaper in the event that shift workers use a couple of terminals. You must create a model of the actual usage. Combining different types of devices is acceptable however it can make management more difficult.
4. Windows 11 Home is technically and legally incompatible.
Windows 11 Home machines cannot join traditional Active Directory Domains, which is a fundamental characteristic of Windows Server. It would be an illegal licensing violation even if there were an alternative solution. Any device on the client side that requires to authenticate or use services (such as file shares, printing queues, etc.), must run Windows 11 Pro, Enterprise, or Education editions. Windows 11 Pro Enterprise or Education editions are required to run the "windows 2025" server. This means that purchasing a Windows 11 home key` for any business machine an unwise investment, if a the server's future deployment is a possibility.
5. The Security Management Nexus – Server, CALs, and Endpoint Security
A properly implemented Windows Server environment with CALs can enable centralized deployment of security policies via Group Policy. It can reduce the cost and hassle of maintaining the standalone security program. In order to avoid the hassle of configuring Kaspersky Premium and Norton 360 on every 50 devices, the policies are able to push configurations that are consistent from the server. This server can manage your endpoint investment which makes it more efficient and efficient. The CAL license is what enables the managed connection.
6. The Office License Synergy in a Server Environment.
Your users are likely to be able to access documents that you share with your windows 2025 server. Microsoft 365 will impact your choice between a perpetual Office 2021 license and an office lizenz. Microsoft 365 Business Premium/Enterprise includes Azure AD that can sync up with your Active Directory on-premise, as and Intune for managing devices. This creates a hybrid model of identity, which makes it simpler to secure and effortless access to cloud-based resources (Microsoft 365 applications) and files on-premise (Server 2025). Subscriptions typically provide a more seamless integration than perpetual licenses.
7. Alternative License for Public Access with "External Connector".
CALs apply only to only internal users. If you'd like to grant other users access to servers (e.g. anonymous FTP or web users) you can't use CALs. Windows Server External Connector License (EC) is required in lieu. It's a license that attaches to the server, and allows unlimited access for unidentified users from outside. Knowing this distinction can prevent massive compliance violations when deploying public-facing services.
8. The CALs are a particular version, but they are compatible with the latest.
You can purchase CALs to access a server that runs a particular version of Windows (e.g. Windows Server CALs 2025). These CALs can be used to connect servers running the particular version or any earlier version. Thus, 2025 CALs grant access to 2025, 2022 or 2019 server. However, later versions will not be supported. When you upgrade "Windows Server 2029", you will need to buy new CALs. This must be factored into the long-term IT budgeting.
9. Virtualization and CALs "Every Access Rule"
Virtualized environments require CALs, however they are based on the access to the virtual machine, not on the virtual machine itself. If you anticipate that 50 users will be using a file-sharing service that is run on a Windows Server 2025 instance, you'll need 50 User Licenses (or enough Device Licenses to cover their devices). The number of virtual servers you manage doesn't directly add up the CALs required; it is the number of users that access the VMs. This makes it easier to avoid buying too much for complex virtual setups.
10. The Total Cost of Ownership (TCO) Realism: Beyond the Server Sticker Price.
Windows Server 2025's business case should include a complete licensing stack. This includes server licenses and the CALs required per device or user, as well as an upgrade of the client PCs if necessary to Windows 11 Pro. This initial capital expense for licenses plus the operating costs of running the server needs to be calculated in relation to a cloud-based solution (like transfer of files to SharePoint within Microsoft 365 or using Azure AD). For small and medium-sized enterprises, cloud subscriptions are more affordable than buying server hardware and paying for Windows Server 2025 licensing. The choice is both architectural and financial, not merely technical. See the most popular office lizenz for site advice including microsoft office download, windows office, microsoft 365 key, microsoft office 2019, microsoft visio software, visio download, office key, key 365 office, windows office, microsoft 365 key and more.


